About This Document>>
Installing SSH Tectia Client >>
Getting Started >>
Connecting to a Remote Host
Defining Quick Connect Options
Generating Keys
Key Generation Wizard
Key Generation - Start
Key Generation - Key Properties
Key Generation - Generation
Key Generation - Enter Passphrase
Key Generation - Finish
Enrolling Certificates >>
Uploading Your Public Key >>
Using Public-Key Authentication with SSH Accession Lite >>
Examples of Use
Configuring SSH Tectia Client >>
Connecting to a Remote Host Computer>>
Transferring Files>>
Tunneling Applications>>
GUI Reference>>
Troubleshooting >>
Command-Line Tools >>
|
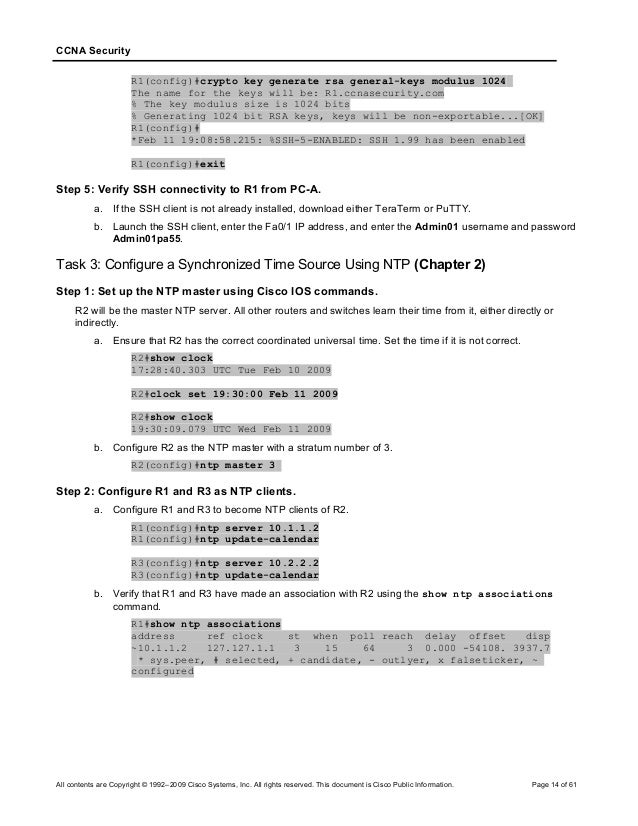
Generating Keys
If you are going to connect to a remote host computer using public-key authentication, you will have to generate a key pair before connecting.
Public-key authentication is based on the use of digital signatures. Each user creates a pair of key files. One of these key files is the user's public key, and the other is the user's private key. The server knows the user's public key, and only the user has the private key.
On the Wolfram User Portal webpage:. Go to. Mathematica 11.3 for mac activation key generator online. If you have a Wolfram ID and know your password, enter your Wolfram ID and Password under Log in with Wolfram ID. Wolfram Alpha’s long-term goal is to make all systematic knowledge computable and broadly accessible. Procedure Downloading Mathematica.
When the user tries to authenticate, the server checks for matching public keys and sends a challenge to the user end. The users are authenticated by signing the challenge using their private keys.
Remember that your private key file is used to authenticate you. Never expose your private keys. If anyone else can access your private key file, they can attempt to log in to the remote host computer as you, and claim to be you. Therefore it is extremely important that you keep your private key file in a secure place and make sure that no one else has access to it.
Do not use public-key authentication on a computer that is shared with other users. Generate keys only on your personal computer that no one else can access!
It also protects you from different types of viruses that can affect your privacy. Hide My IP Crack Premium License Key Free Plus Torrent Windows 10 64bitMoreover, this application automatically configures your internet browser from a non0public proxy network. Above all, it features versatile preview and highly custo-mizable with dual panes interface. Now day’s cyber attacks are increasing so this application protects you from falling prey to these attacks. Hide my ip serial key generator.
Also note that if you are using the Windows roaming profiles functionality, your personal settings will be replicated with the roaming profile server. If you store your private keys in the default location (under the profile folder of your Windows user account) your private keys may be susceptible to a malicious user listening to the network traffic. Therefore the User Settings folder should not be a directory that is used in profile roaming.
In order to use public-key authentication, you must first generate your own key pair. You can generate your own key files with the help of a built-in Key Generation wizard.
You can also import existing keys on the Keys page of the Settings dialog. See Section Managing Keys.
Key Generation Wizard
Key Generation - Start
Key Generation - Key Properties
Key Generation - Generation
Key Generation - Enter Passphrase
Key Generation - Finish