Group Secret Key Generation Algorithms
In order to generate a group secret key in the multiuser network, we propose an algorithm through all users' collaboration and using the wireless signal strength. Three specific investigations are. The shared key k is concatenated to the end of the initialization vector (IV) v, forming. Is then used as the input to the RC4 algorithm to generate a keystream RC 4 ( v, k ). The plaintext P is exclusive-or’ed (XOR, denoted by ⊕) with the keystream to obtain the ciphertext: C = P ⊕ RC4 (v,k).
Key generation is the process of generating keys for cryptography. The key is used to encrypt and decrypt data whatever the data is being encrypted or decrypted.
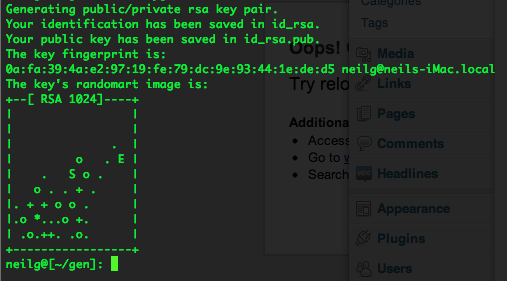
Modern cryptographic systems include symmetric-key algorithms (such as DES and AES) and public-key algorithms (such as RSA). Symmetric-key algorithms use a single shared key; keeping data secret requires keeping this key secret. Public-key algorithms use a public key and a private key. The public key is made available to anyone (often by means of a digital certificate). A sender will encrypt data with the public key; only the holder of the private key can decrypt this data.
Since public-key algorithms tend to be much slower than symmetric-key algorithms, modern systems such as TLS and its predecessor SSL as well as the SSH use a combination of the two in which:
- One party receives the other's public key, and encrypts a small piece of data (either a symmetric key or some data that will be used to generate it).
- The remainder of the conversation (the remaining party) uses a (typically faster) symmetric-key algorithm for encryption.
The simplest method to read encrypted data is a brute force attack–simply attempting every number, up to the maximum length of the key. Therefore, it is important to use a sufficiently long key length; longer keys take exponentially longer time to attack, making a brute force attack invisible and impractical.
Currently, commonly used key lengths are:
- 128-bits for symmetric key algorithms.
- 1024-bits for public-key algorithms.
Key generation algorithms[changechange source]
In computer cryptography keys are integers. In some cases keys are randomly generated using a random number generator (RNG) or pseudorandom number generator (PRNG), the latter being a computeralgorithm that produces data which appears random under analysis. Some types the PRNGs algorithms utilize system entropy to generate a seed data, such seeds produce better results, since this makes the initial conditions of the PRNG much more difficult for an attacker to guess.
In other situations, the key is created using a passphrase and a key generation algorithm, using a cryptographic hash function such as SHA-1.
Related pages[changechange source]
- Distributed key generation: For some protocols no party should be in the sole possession of the secret key. Rather, during distributed key generation every party obtains a share of the key. A threshold of the participating parties need to work together in order to achieve a cryptographic task, such as decrypting a message.
References[changechange source]
Key generators are constructed using one of the getInstance class methods of this class.
KeyGenerator objects are reusable, i.e., after a key has been generated, the same KeyGenerator object can be re-used to generate further keys.
Windows 10 pro product key generator online. Dec 19, 2017 Go to the Microsoft Site for Buying windows 10 key generator 2019. The Price of this Product key is almost $199. The best part is that you can purchase windows 10 pro product key for the lifetime. When you Upgrade to Windows 10 from Windows 7, even you can use Windows 10 Professional Product Key Generator. Windows 10 Product Key Generator is the greatest practical tool to activate not registered Windows 10 Pro, Enterprise, Home and other editions. It saves your time to discovery useful or working product keys for 32bit and 64bit windows. It the relief to remove watermark or notice from windows. Jan 29, 2020 Windows 10 Pro Product Key Generator Free Download Windows 10 professional edition is always recommending to activate for full version. Nov 01, 2019 Windows 10 Product Key Generator Online saves time to detection working or useful product keys for both 32bit and 64bit windows. It the aid to eliminate watermark or detect from windows attributes. It the aid to eliminate watermark or detect from windows attributes. Apr 02, 2020 Windows 10 Product Key Generator With Activator 2019 For 32&64 Bit. Windows 10 Product Key Generator is the most essential and useful working tool that is downloaded to deal with the entire Window Activation process.
There are two ways to generate a key: in an algorithm-independent manner, and in an algorithm-specific manner. The only difference between the two is the initialization of the object:
- Algorithm-Independent Initialization
All key generators share the concepts of a keysize and a source of randomness. There is an
initmethod in this KeyGenerator class that takes these two universally shared types of arguments. There is also one that takes just akeysizeargument, and uses the SecureRandom implementation of the highest-priority installed provider as the source of randomness (or a system-provided source of randomness if none of the installed providers supply a SecureRandom implementation), and one that takes just a source of randomness.Since no other parameters are specified when you call the above algorithm-independent
initmethods, it is up to the provider what to do about the algorithm-specific parameters (if any) to be associated with each of the keys. - Algorithm-Specific Initialization
For situations where a set of algorithm-specific parameters already exists, there are two
initmethods that have anAlgorithmParameterSpecargument. One also has aSecureRandomargument, while the other uses the SecureRandom implementation of the highest-priority installed provider as the source of randomness (or a system-provided source of randomness if none of the installed providers supply a SecureRandom implementation).
National Secret Algorithm
In case the client does not explicitly initialize the KeyGenerator (via a call to an init method), each provider must supply (and document) a default initialization.
Every implementation of the Java platform is required to support the following standard KeyGenerator algorithms with the keysizes in parentheses:
- AES (128)
- DES (56)
- DESede (168)
- HmacSHA1
- HmacSHA256