Admt Unable To Generate Encryption Key
KB ID 0001306
Problem
Active Directory Migration Toolkit (ADMT) Walkthrough Leave a reply Active Directory Migration Toolkit (latest version is v3.2) is a free tool that allows both Inter-Forest and Intra-Forest user, group and computer migration. Active Directory Migration Toolkit (ADMT) Walkthrough Leave a reply Active Directory Migration Toolkit (latest version is v3.2) is a free tool that allows both Inter-Forest and Intra-Forest user, group and computer migration.
Back in Part One we setup our migration admin account, and installed ADMT. Now, as I’m going to migrate the users passwords I need a ‘Password Export Server‘, but first I need to tackle the subject of user SIDs
Solution
Domain Migrations and SID Filtering
Every user has a SID (Security Identifier) it’s the thing AD uses to refer to and apply security to users, (and other objects). This is why you can rename a user and it’s security does not change, (because the SID always remains the same). Why is this important for domain migrations? Well if you’re a doing a migration that’s taking place over a period of time, users in the NEW domain may still need access to things IN the OLD domain, (like file shares, printers, applications etc).
This is a problem because when you setup a domain trust it Enables SID filtering, back in part one it told you this, here. So if a user in newdomain.com tries to access a folder, (they could access before the migration,) in olddomian.com they wont be able to do so, (because their SID has changed, to a new SID in the new domain. Even if you migrated their old SID if get’s filtered out as the user comes back over the trust).
How do we fix that? We need to do two things,
- Migrate the users old SID to newdomain.com (This then become their, sIDHistory attribute)
- Disable SID filtering in olddomain.com (To allow the sIDHistory attributes to come back over the trust)
This lets users in the new domain have their NEW SID, and their OLD SID.
Migrating the users SID is simple, (it’s just a box you tick when running a migration, you will see that later). Disabling SID filtering can be a little confusing. Where do you do it, and which way round do you execute the command? Above I’ve solved the first one for you you Disable SID Filtering on the OLD domain. The following diagram will explain why;
Usually users DON’T have a sIDHistory. attribute, (unless they’ve been migrated before!) They only have a SID (objectSID attribute.) To demonstrate let’s jump forward in time, and look at a migrated user (ABarksdale)
Click to enlarge the above image, and inspect the users SID (objectSID) and old SID (sIDhisttory) attributes.
In the olddomain.com;
objectSID: S-1-5-21-227018303-3265311450-382577
sIDHistory: {None}
In the newdomain.com;
objectSID: S-1-5-21-3846632479-19853633304-4016520
sIDHistory: S-1-5-21-227018303-3265311450-382577 (Note: objectSID migrated from olddomain.com)
Disabling SID Filtering
Now we know where to do it, we just need to construct the command to disable it. Run the following command;
Or for a Forest Trust
So in my example;
- source-domain: olddomain.com
- target-domain: newdomain.com
- username: (Domain administrator in olddomain.com)
- password: Password for user above.
ADMT: Setting up a Password Export Server
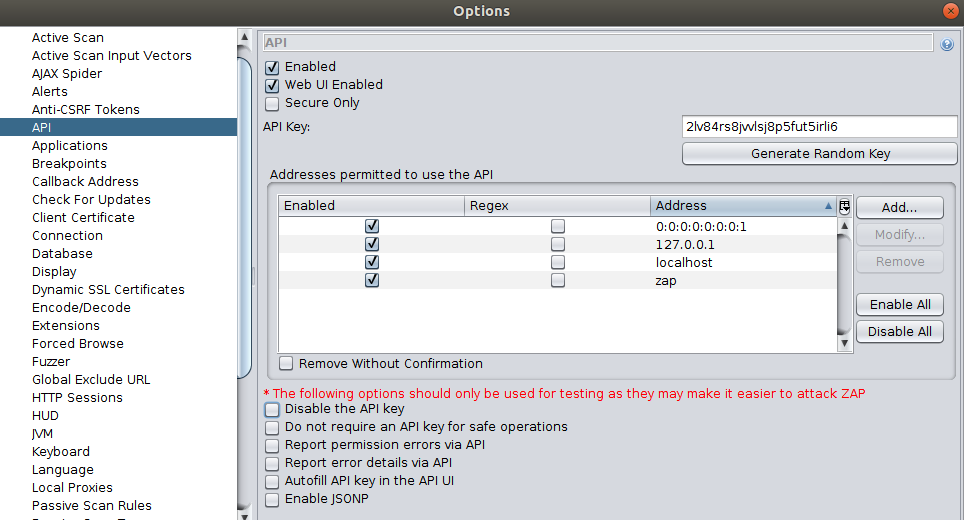
As the name implies, this is a piece of software that runs on the source domain, (on a domain controller,) that ADMT uses to migrate user passwords. Before you can do this, you need to create a ‘key’ in the NEW domain, (where ADMT is running). Then, you use that key to setup the password export server in the OLD domain.
On the ADMT Server open an administrative command window and issue the following command;
So in my example;
- source-domain: olddomain.com
- keyfile: Where you want to save the keyfile.
- password: can be anything you want, but you will need it to setup the password export server, so don’t forget it.
If it runs OK, find your keyfile, then copy this to the domain controller in the old domain you are going to install the password export server service on.
Theres two versions of the password export server software, (a 32 bit and a 64 bit version.) Download and install the version applicable to your source domain controller.
Note: The install requires a reboot of the server, you might want to do this at the end of the day.
The install is pretty simple, Accept the EULA, browse to the keyfile, and enter the password you used above.
SAP NetWeaver 7.0 EHP2: SAP License Key. SPS22. Versions. Fetch the new network ID of each ID generator by using the IP address of the message server and the port with the script sapcontrol. Check with transaction SLICENSE of AS ABAP, with the Visual Administrator, or with SAP NetWeaver Administrator, whether the system is using the. I have downloaded and installed SAP NetWeaver Application Server ABAP 7.02 SP6 32-bit Trial Version from the SAP Store. While trying to generate a license key, the SAP is asking for a hardware key. J2EE Engine stand alone or Enterprise Portal EP6 SP3 - SP8 license keys should be installed using the Visual Administrator/SAP NetWeaver Administrator. License keys with SWPRODUCTNAME NetWeaver in the license key file are not valid in the Visual Administrator/SAP NetWeaver Administrator. Move SAP NetWeaver Enterprise Portal from one server to another. The SAP license key depends on the machine identification number. After initial installation you need to activate your license/installation. If you already have an activation code, follow the steps below. If you do not have an. SAP license key SAP temporary license. Sap netweaver license key generator free.
Specify a user account to run the service as, (I just use the ADMTAdmin account we’ve already created).
Finish the install, and let it reboot.
After a reboot, if you look in the services (Start > Run > services.msc). You will see the ‘Password Export Server Service’.
Note: You will also notice the startup type for the service is ‘Manual’. ONLY start this service, when you are actually migrating passwords.
ADMT: Granting Local Rights to ADMT user in the Source Domain.
To migrate machines, the ADMTAdmin user needs “Local” administrative access on all the source machines. The easiest way to do this is via group policy, using ‘Restricted Groups’. This allows you to take a group (or user) and put put them on the local groups (including administrators) of the targeted machines.
In the OLD domain, create a group and put the ADMTAdmin from the target domain in it. (I put the domain admin from the target domain in it as well, to be on the safe side, but that’s up to you).
Note: You may see this a few times while doing migrations, notice above the user icon there’s a small red curved arrow (below), that logo denotes ‘Foreign Security Principle’, it’s not really our user at all, it’s a special object that AD creates in a hidden OU, (turn on advanced mode in AD users and computers you can see them.)
Create a new GPO that will apply to the computers/servers you are going to migrate.
Edit it.
Navigate to;
Add a new one, select the group you have just created > and add it to ‘Administrators’.
It should look like this when you are finished.
To test it has applied, on a client run ‘gpresult -R’ at an administrative command prompt.
You can of course, simply check the local administrators group to make sure the new group is in there.
ADMT: Additional GPO Note
To perform computer migrations, (and security translations), ADMT needs to deploy an ‘agent’ to the machines in the OLD domain. The local firewall (if enabled) can stop this, I simply disable the local firewall. (If someone wants to send me a list of ports to add, to make it work I’ll publish the). But even the Microsoft Documentation on Technet says disable the firewall.
Create a new GPO linked to where your source computers are, (here I’m just linking to the root of the domain).
Edit the GPO.
Navigate to;
Locate “Windows Firewall protect all network connections‘ and set it to disabled.
In addition I have also seen the agent fail to deploy if the ‘Remote Registry Service’ is not running on the target machines, (it’s disabled by default). So I use this policy to turn that on as well.
In the same GPO navigate to;
Locate the ‘Remote Registry’ service, and set it’s startup to automatic.
This may take a while to permeate down to all the machines, Windows – Forcing Domain Group Policy
In Part Three we will start migrating objects.
Related Articles, References, Credits, or External Links
NA
-->Creating and managing keys is an important part of the cryptographic process. Symmetric algorithms require the creation of a key and an initialization vector (IV). The key must be kept secret from anyone who should not decrypt your data. The IV does not have to be secret, but should be changed for each session. Asymmetric algorithms require the creation of a public key and a private key. The public key can be made public to anyone, while the private key must known only by the party who will decrypt the data encrypted with the public key. This section describes how to generate and manage keys for both symmetric and asymmetric algorithms.
Symmetric Keys
The symmetric encryption classes supplied by the .NET Framework require a key and a new initialization vector (IV) to encrypt and decrypt data. Whenever you create a new instance of one of the managed symmetric cryptographic classes using the parameterless constructor, a new key and IV are automatically created. Anyone that you allow to decrypt your data must possess the same key and IV and use the same algorithm. Generally, a new key and IV should be created for every session, and neither the key nor IV should be stored for use in a later session.
To communicate a symmetric key and IV to a remote party, you would usually encrypt the symmetric key by using asymmetric encryption. Sending the key across an insecure network without encrypting it is unsafe, because anyone who intercepts the key and IV can then decrypt your data. For more information about exchanging data by using encryption, see Creating a Cryptographic Scheme.
The following example shows the creation of a new instance of the TripleDESCryptoServiceProvider class that implements the TripleDES algorithm.
When the previous code is executed, a new key and IV are generated and placed in the Key and IV properties, respectively.
Sometimes you might need to generate multiple keys. In this situation, you can create a new instance of a class that implements a symmetric algorithm and then create a new key and IV by calling the GenerateKey and GenerateIV methods. The following code example illustrates how to create new keys and IVs after a new instance of the symmetric cryptographic class has been made.
When the previous code is executed, a key and IV are generated when the new instance of TripleDESCryptoServiceProvider is made. Another key and IV are created when the GenerateKey and GenerateIV methods are called.
Asymmetric Keys
The .NET Framework provides the RSACryptoServiceProvider and DSACryptoServiceProvider classes for asymmetric encryption. These classes create a public/private key pair when you use the parameterless constructor to create a new instance. Asymmetric keys can be either stored for use in multiple sessions or generated for one session only. While the public key can be made generally available, the private key should be closely guarded.
A public/private key pair is generated whenever a new instance of an asymmetric algorithm class is created. After a new instance of the class is created, the key information can be extracted using one of two methods:
The ToXmlString method, which returns an XML representation of the key information.
The ExportParameters method, which returns an RSAParameters structure that holds the key information.
Admt Unable To Generate Encryption Key In Excel
Both methods accept a Boolean value that indicates whether to return only the public key information or to return both the public-key and the private-key information. An RSACryptoServiceProvider class can be initialized to the value of an RSAParameters structure by using the ImportParameters method.
Asymmetric private keys should never be stored verbatim or in plain text on the local computer. If you need to store a private key, you should use a key container. For more on how to store a private key in a key container, see How to: Store Asymmetric Keys in a Key Container.
The following code example creates a new instance of the RSACryptoServiceProvider class, creating a public/private key pair, and saves the public key information to an RSAParameters structure.